Risky Biz News: BPF malware is now a thing
In other news: Russia to block calls from spoofed numbers; macOS to block unknown USB-C devices; and a new Tesla car hack.
This newsletter is brought to you by Airlock Digital, Rumble Network Discovery, Proofpoint, and Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed.
Over the past several months, threat actors appear to have taken a liking to developing malware that abuses the Berkeley Packet Filter (BPF) as a way to silently backdoor Linux-based systems.
Created in the early 90s, the BPF is a technology on *NIX-based systems that can allow the OS and locally installed applications to intercept and analyze network traffic. In most cases, the BPF is enabled by default, especially on Linux and BSD systems used as servers, where the BPF plays a key role in firewalls and other security tooling.
The first and most widely-known case where the BPF was used in the design of a malware strain was in 2017; when the Shadow Brokers leak exposed tools developed by the Equation Group (supposedly the US National Security Agency) that used BPF filters as a way to create hidden communications channels between infected hosts and C&C servers [see DewDoor and Bvp47 reports].
But over the past year, several threat actors have also looked closer at BPF and have developed their own tools that abuse it in their attacks.
The most widely known example is BPFDoor, a malware strain first spotted by PwC and first documented in its 2021 year in review report, published a month ago. PwC linked the backdoor to a Chinese nation-state group named Red Menshen, an attribution later confirmed by CrowdStrike in a separate report [BPFDoor is called JustForFun in their report, and Red Menshen is LightBasin].
Technical reports from Elastic's security team, ExaTrack [PDF], Sandfly Security, and security researcher Kevin Beaumont describe BPFDoor as a passive backdoor that hooks into the BPF service, which it then (ab)uses to listen to commands sent via network packets. When a command is received, the malware executes it on the underlying OS.
The PwC report claims that BPFDoor has been in use for at least five years, putting its development just around the Shadow Brokers leak, which might suggest that the Chinese group has closely studied the leak tooling for new techniques and almost immediately weaponized them.
But five years is a hell of a lot of time in the cybersecurity business. Something like this should have been detected a long time ago—except Beaumont has a very good reason why it has not:
"Because BPFDoor doesn't open any inbound network ports, doesn't use an outbound C2, and it renames its own process in Linux (so ps aux, for example, will show a friendly name) it is highly evasive."
In addition, there's also the problem of the Linux security tooling ecosystem, which is nowhere near as crowded as the Windows sphere. The Linux security tools that exist simply didn't think to look at the BPF, something that was pointed out by multiple infosec experts on social media once BPFDoor came to light. Since then, cybersecurity firms have been working hard to correct this issue, and some have been on the hunt for similar BPF threats.
At the RSA conference this week, BlackBerry and Intezer researchers showcased the fruits of their recent labors. The two companies unveiled Symbiote, another silent backdoor for Linux systems that abuses the BPF.
"Symbiote and BPFDoor are two different malware strains," an Intezer spokesperson told Risky Business News in an email earlier this week.
"While both are using BPF, the end goal is different. BPFDoor opens a raw socket and uses BPF to filter (packet capture) network packets with magic values that are used for its command and control. This allows the malware to process the command and control network packets without attaching the socket to a specific port."
"Symbiote uses BPF to hide traffic from someone that investigates an infected machine. If an admin, for example, starts a packet capture for all TCP traffic using tcpdump on the infected machine, tcpdump generates
BPF bytecode that is injected into the kernel. Symbiote captures this action and adds its own code bytecode first to remove the traffic it doesn't want the admin to see. So while the admin asks for all TCP packets to be captured, Symbiote ensures that only TCP packets not belonging to the traffic it wants to hide are captured."
But besides how the two malware strains were designed, their use also appears to be different. For example, BPFDoor was linked to a Chinese five-year-old cyber-espionage operation. Beaumont said it discovered the malware installed on government systems, postal and logistic systems, education systems, and more; in countries such as the US, South Korea, Hong Kong, Turkey, India, Vietnam, and Myanmar.
On the other hand, BlackBerry and Intezer researchers said that Symbiote was used in attacks against the financial sector in Latin America and that based on the domains used by the malware, they believe the attackers were impersonating Brazilian banks and the local federal police.
The somewhat sad conclusion of both reports is that the Linux security landscape is in a very bad state right now if passive backdoors that tap into the raw networking service go undetected for five years, for a technique that has been so widely abused by Windows malware for many years, an opinion also shared by The Grugq in his newsletter. Nonetheless, at least for now, the infosec industry appears to have been put on notice about this particular technique, yet, judging by the comments people are making on social media, detection on Linux systems still appears to be years behind compared to what's currently detectable on Windows systems.
Breaches and hacks
Osmosis hack: The operators of the Osmosis cryptocurrency platform have suspended operations this week after a threat actor used an exploit to steal approximately $5 million from its liquidity pools. The company said the exploit did not impact all of its funds and was working to restore service.

Optimism hack: In one of the most facepalm-worthy crypto-hacks of all time, the Optimism cryptocurrency project said it lost $19 million worth of funds after one of its partners sent funds to an Ethereum wallet they didn't yet have full control of. The cringeworthy IR report is here, and, according to Motherboard, the Optimism project is now pleading with the person who spotted and hijacked the errant transfer to return some of the stolen funds.
Mobike leak: Bike-sharing service Mobike leaked the passports, driver's licenses, and identity documents of more than 120,000 customers. Almost all of the identity documents were for users in Latin America, including Argentina and Brazil, TechCrunch reported, which worked for months with the vendor to have the leaky server secured.
TheTruthSpy leak: TheTruthSpy, a quite popular stalkerware app, also left servers exposed on the internet. Per Motherboard, the company leaked data from smartphones where the app was installed. Leaked data included photos of children, pets, and others related to babies, per the news outlet.
Kommersant FM hacked: An unidentified threat actor breached the network of Russian radio station Kommersant FM on Wednesday. The hacker broadcast the Ukrainian national anthem and anti-war songs to protest Moscow's invasion of Ukraine. Kommersant confirmed the hack, shut down its airwave broadcast, and moved to internet streaming until the issue was resolved.
A positive side to ransomware: After a ransomware attack, the Tenafly Public School District in New Jersey canceled all final exams this year.
General tech and privacy
macOS and USB-C: At the WWDC 2022 conference this week, Apple announced that macOS Ventura will block unknown USB-C devices from communicating with macOS until the user has specifically approved the device. macOS Ventura is the next iteration of Apple's macOS desktop operating system and is set to be released this fall.
Apple wins class-action: A California judge dismissed a class-action lawsuit filed against Apple in regards to its devices being vulnerable to the Meltdown and Spectre vulnerabilities, Reuters reported. The lawsuit argued that plaintiffs "overpaid for their devices because Apple knowingly concealed defects, and provided security patches that made its devices significantly slower."
New Microsoft Defender feature: Microsoft has rolled out a new feature to its Defender for Endpoint product that will now allow system administrators to isolate compromised devices from having any form of communications with any other device in the same network.
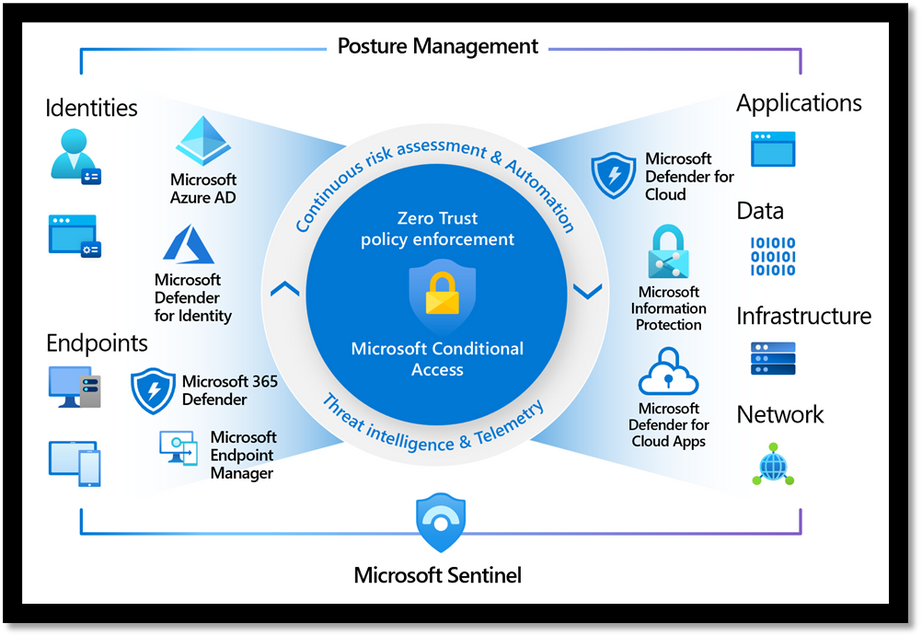
Microsoft security products: Need help understanding Microsoft's security products? Don't answer that. Of course, you do. Everyone does. So here's an overview from Microsoft itself.
Government, politics, and policy
GAO annual weapons systems assessment: In its annual review of the US' weapons systems, the Government Accountability Office found that the DOD is lagging behind in adopting modern software and the implementation of basic cybersecurity best practices. They probably copy-pasted this part from the previous years. Full report here [PDF]. Press coverage here.
Israel lobbying for NSO Group: Axios reported on Wednesday that Israeli government officials have lobbied the US government to have spyware maker NSO Group removed from its sanctions list. The news comes as NSO Group is having an increasingly harder time paying employees after the US sanctions have cut into its profits.
Russia to block calls from spoofed numbers: The Russian government is preparing legislation that will mandate that mobile operators detect and block phone calls made via spoofed numbers. According to Russian news outlet Kommersant, mobile operators will have to install systems developed by the Main Radio Frequency Center (GRFC), a subdivision of the Roskomnadzor telecommunications watchdog, that will verify caller identities. All calls will go through these systems, which will operate similarly to the SORM system used by the Russian government to monitor internet traffic. Sounds like national surveillance disguised as a "customer security issue," but what do I know.
Cybercrime and threat intel
Burkov case: A Forbes investigation discovered that US law enforcement agencies used secret court orders to force two of the world's largest travel companies—Sabre and Travelport—to continuously monitor the movements and travels of Aleksei Burkov, the Russian hacker behind the CardPlanet carding forum. The secret surveillance took place for two years until authorities detained Burkov during a vacation in Tel Aviv.
Facebook phisher uncovered: Cybersecurity firm PIXM said it identified the true identity of a cybercriminal who has lured hundreds of millions of Facebook on phishing sites in an attempt to collect their credentials. The company said the threat actor has been active since September 2021, has successfully collected at least 1 million credentials over the past months, and the entire phishing operation appears to be linked to a Colombian company selling access to "Facebook like bots." PIXM said it shared its findings with both Colombian authorities and Interpol.
DDoS attacks on Russia: DDoS mitigation services Radware and DDoS-Guard have reported a huge increase in the number of DDoS attacks targeting Russian companies. Both companies attributed most of the attacks to hacktivist activity following Russia's invasion of Ukraine.
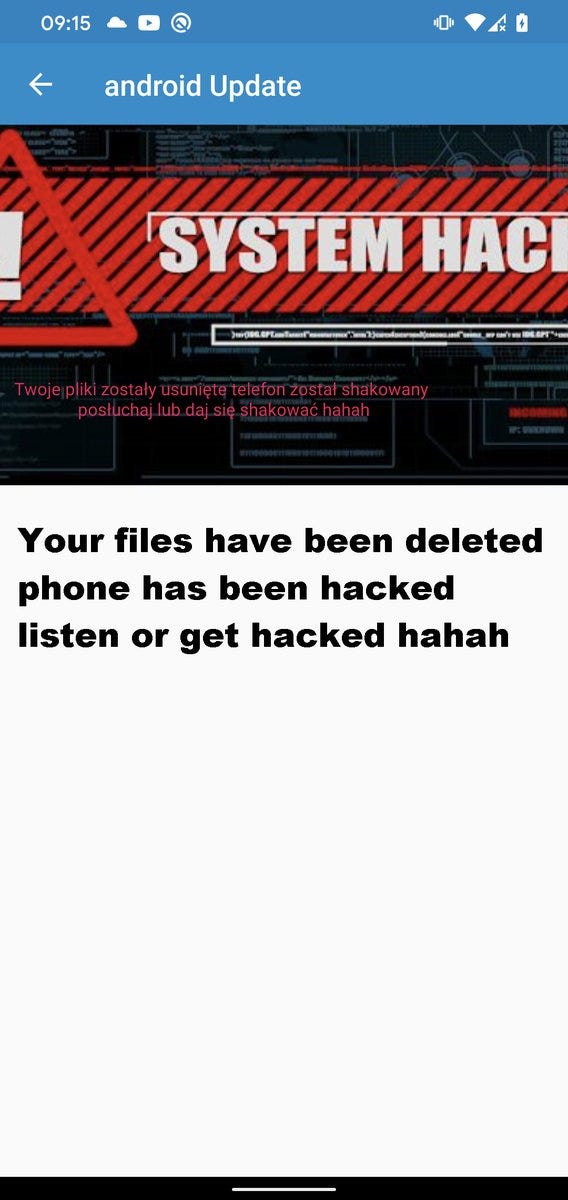
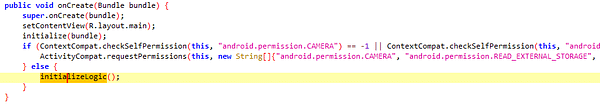
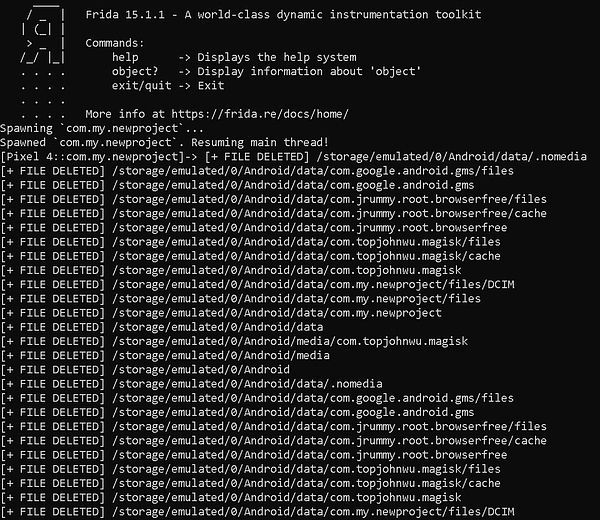
Android wiper discovered: Independent security researcher MalwareHunter has discovered this week a malware strain designed to wipe the external storage of Android devices.



Ransomware trends: A Cybereason study on more than 1,400 organizations across the globe found that 80% of companies that were hit by a ransomware attack were also hit for a second time due to improper recovery and incident response efforts. The company said that 68% of the companies that got hit for a second time said the second attack came less than a month after the first, and threat actors demanded a higher ransom payment.
Decrypter sold on Roblox store: Security researcher MalwareHunter has discovered a new ransomware strain that uses the Roblox game store to sell access to its decrypter. [Coverage in Bleeping Computer]
Card fraud prediction: Recorded Future's Gemini Advisory seems to think that the recent Ruso-Ukrainian conflict will lead to an increase in payment card fraud as members of Russia's large and highly skilled IT community will seek to supplement or replace lost and legitimate income through cybercrime, including the compromise and sale of payment cards.
Arrests in Japan: Japanese authorities have detained two men who hacked into the servers of a web production company and deleted some of its data. The intrusion, which took place last November, led to outages and downtimes for more than 1,000 websites, according to Japanese media.
Malware technical reports
Cuba ransomware: Trend Micro reported this week that the Cuba ransomware gang has resurfaced with a new version of their ransomware, optimized with new infection techniques. The ransomware was first spotted in February 2020, and it saw a huge spike in activity throughout 2021 [PDF], when the FBI said the gang made around $43.9 million from attacks against at least 49 organizations.
FakeCrack: Avast published a report on FakeCrack, a malware distribution campaign using black-hat SEO to push malware-laced versions of the CCleaner software.
Smilodon: The Smilodon web skimming operation has shifted its focus from targeting Magento stores to online shops hosted on WordPress' WooCommerce plugin, Sucuri said on Thursday.
LockBit: Palo Alto Networks has a report out on LockBit, today's most active ransomware gang.
APTs and cyber-espionage
Aoqin Dragon: SentinelOne has published a report on a new suspected Chinese APT named Aoqin Dragon. Per the report, this threat actor has been targeting government, education, and telecommunication organizations in Southeast Asia and Australia since at least 2013. One of the campaign's hallmarks—using pornography as a lure. Classic!
Vulnerabilities and bug bounty
Tesla car hack: Apparently, when you unlock your Tesla car with the company's new NFC-based keys, the car is also put in a state where attackers can also silently enroll their own keys with no authentication required or UI alert for the car owner. Obviously, this can be abused in a bazillion ways. More in ArsTechnica.
Bluetooth tracking research: A team of academics from the University of California, San Diego, has demonstrated for the first time that Bluetooth signals emitted constantly by modern smartphones or other smart devices have a unique fingerprint that can be used to track individuals' movements. The full research paper is here [PDF].
GCP vulnerability: Google said in a blog post this week that it will roll out patches for all customers by late August to fix a vulnerability in the Google Kubernetes Engine (GKE) for all Google Cloud Platform customers. The vulnerability, discovered through Google's public bug bounty program, would allow attackers to breach customer firewalls and access the GKE API server IP address directly off the internet and without any authentication.

PHP RCEs: Shared hosting providers, please take note!


Infosec industry
New Chrome research: CyberArk researchers have published new research this week detailing a new technique to extract cleartext credential data—such as usernames, passwords, and site URLs—from Chrome's memory. Cookies can also be stolen with this technique, putting online accounts protected by 2FA at risks of hijacking, researchers said.
DigiCert acquires DNS Made Easy: Certificate authority DigiCert announced on Thursday that it acquired DNS Made Easy, a managed Domain Name System (DNS) service provider.
NahamCon 2022 videos: Talks from the NahamCon 2022 are available on YouTube.