Risky Biz News: Cybercrime crew infects 172,000 smart TVs and set-top boxes
In other news: Invati Connect Secure zero-days enter mass exploitation; more than 178,000 SonicWall firewalls still unpatched; and Citrix patches two new zero-days.
This newsletter is brought to you by Panther, the scalable detection-as-code based SIEM. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed. On Apple Podcasts:
A cybercrime operation is believed to have infected at least 172,000 smart TVs and set-top boxes with malware that carries out DDoS attacks.
Named Bigpanzi, the group has been active since at least 2015 and appears to target Spanish and Portuguese-speaking users across Latin America.
According to Chinese security firm QiAnXin, Bigpanzi built its botnet through social-engineering tactics, such as spreading apps to view pirated content, apps to enhance TV viewing experiences, and backdoored firmware updates.
Once installed, the apps and firmware updates would ensnare infected devices into the Bigpanzi botnet and carry out attacks at the operator's behest.
QiAnXin says Bigpanzi is the same group behind the Pandora botnet discovered by Russian security firm Dr.Web in September 2023.
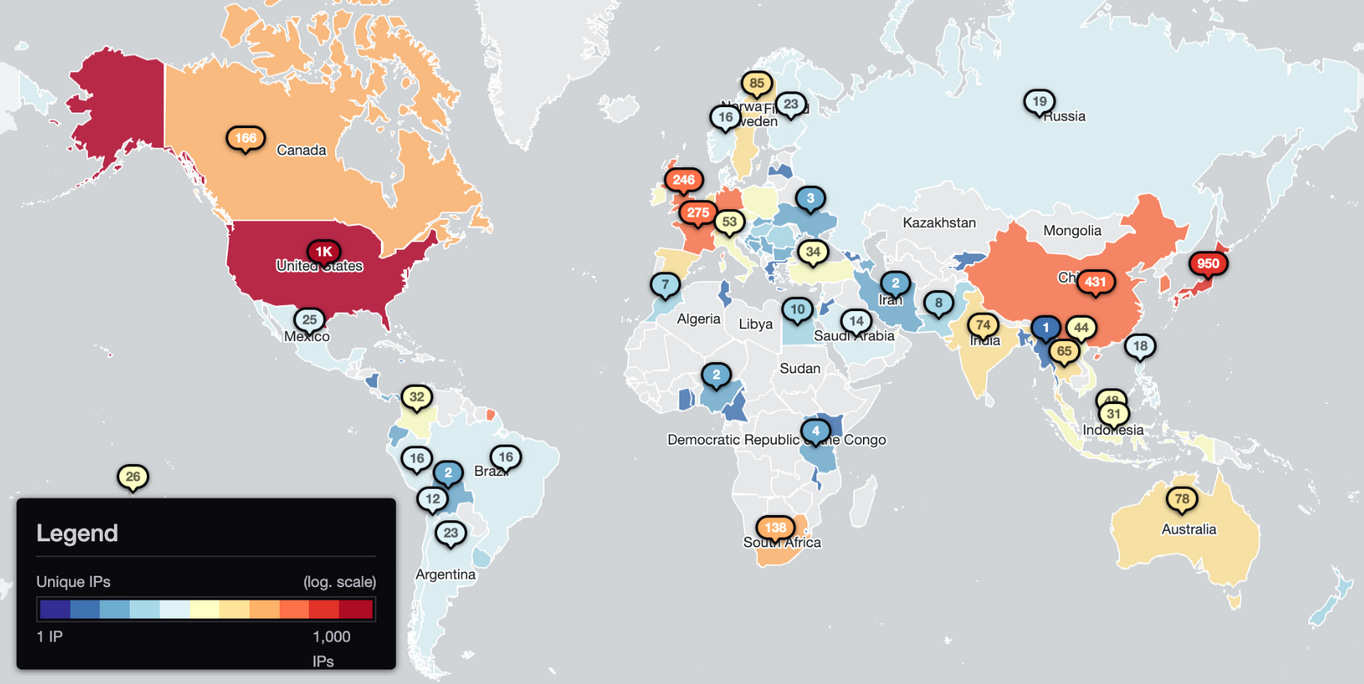
While Chinese researchers say they tracked roughly 172,000 infected devices per week after they managed to hijack two of the botnet's command-and-control domains, they also estimate the Bigpanzi's real size to be in the realm of millions. They believe this because they only intercepted a small section of the botnet's C&C infrastructure and because of the ephemeral nature of smart TVs and set-top boxes, which are not always powered on and connected to Bigpanzi servers.
Researchers say that most of the botnet's infected devices are located in Brazil and are either Android-based smart TVs or TV set-top boxes that run on eCos, an open-source operating system for embedded devices.
Bigpanzi (Pandora) is the latest in a long list of modern-day botnets that specifically target smart TVs and set-top boxes, such as Ares, the Lemon Group, and BADBOX. The last two, and the most recent ones, primarily focus on ad fraud rather than DDoS attacks, which makes Bigpanzi somewhat stand out.
Breaches, hacks, and security incidents
Wise Lending crypto-heist: The Wise Lending DeFi platform has lost $464,000 worth of crypto-assets after an attacker exploited a vulnerability in its smart contract.
Fake Romanian DB leak: A post on the XSS hacking forum claiming to sell the data of more than 21 million Romanians has proven to be fake, according to Bit Sentinel's Andrei Avadanei.
Cloud provider returns stolen data: Cloud service provider Wasabi has returned stolen patient data that was stored on its servers to New York hospital chain North Star Health Alliance. The data had been stored on its servers by the Lockbit ransomware, which hacked the hospital in August 2023. North Star sued the ransomware group and obtained a court order to regain control over the gang's servers. [Additional coverage in HealthcareInfoSecurity]
General tech and privacy
ICO to look at AI scraping: The UK's privacy watchdog is looking at the legality of AI companies scraping web content to train generative models. The initiative will analyze if the practice breaks property or contract laws and its compliance with existing data protection laws.
Crypto firm shuts down after NY fine: Cryptocurrency trading platform Genesis Global shut down operations after receiving an $8 million fine in the US state of New York. Officials fined the company for failing to implement anti-money laundering and cybersecurity programs. The company shuttered its online website hours after receiving the fine. [Additional coverage in The Record]
Google to let EU users unlink services: Google will let European users unlink its services from one another. Some examples:
When Search, YouTube, and Chrome are not linked services, your recommendations in Search, like "What to watch" and your Discover feed will be less personalized.
When Search and Maps are not linked services, Reservations made on Search won’t appear in Google Maps.
Government, politics, and policy
Turkey secretly bans VPNs: The Turkish government has secretly ordered local internet service providers to block access to 16 VPN services. The block was enforced in December, and some of the blocked services include TunnelBear, Surfshark, and CyberGhost. Turkey has had strict control over its internet for years. Besides blocking access to pornographic sites, the country has also blocked access to news sites critical of the country's president, opposition websites, and pro-Kurdish content. The country joins China, Iran, and Russia in formally blocking VPN services. [Additional coverage in FT]
DOD Cyber Red Teams: The US Department of Defense has updated the rules and responsibilities for its cyber red teams [PDF].
UK-Ukraine security cooperation: The British and Ukrainian governments have signed a security cooperation agreement. The document covers both military and cyber matters.
Russia approves IoT protocol: The Russian Technical Regulation and Metrology Agency (Rosstandart) has approved the LoRaWAN protocol as the country's official Internet of Things (IoT) protocol. [Additional coverage in Cnews]
Telegram deanonymization: The Russian government claims it developed an AI system named Comrade Major (Товарищ майор) that can deanonymize the owners of Telegram channels. The system was developed by Russian software company T.Hunter and is expected to be formally launched this year or in 2025. Russian officials say they plan to use the new system for law enforcement. [Additional coverage in Izvestia]
Sponsor section
In this Risky Business News sponsor interview, Tom Uren talks to Ken Westin, Field CISO at Panther, about how the rise of cloud and hybrid IT architectures requires a new type of SIEM.
Cybercrime and threat intel
Tether is a favorite with scammers: The Tether (USDT) cryptocurrency has become the favorite money laundering medium used by pig-butchering groups, according to a recent report from the United Nations Office on Drugs and Crime (UNODC). The UN says the currency is widely used due to its widespread adoption and relatively easy access. Besides pig-butchering scams, Tether is also popular with task scam groups, a new type of scam where users are recruited to perform various online tasks in exchange for commissions. [Additional coverage in FT]
State of Software Supply Chain Security: ReversingLabs has published the 2024 State of Software Supply Chain Security Report, a document outlining major trends in software supply chain security from last year and how they may impact the current year's threat landscape.
A 400% annual increase in threats on the PyPI platform, with more than 7,000 instances of malicious PyPI packages discovered in the first three quarters of 2023. The vast majority of these were classified as "infostealers."
More than 40,000 instances of leaked or exposed development secrets across the major package managers (npm, PyPI, and RubyGems).
Instances of malicious npm packages in the first three quarters of 2023 decreased by 43% compared with malicious npm packages identified in all of 2022.
Npm accounted for 77%, or 31,000, of the more than 40,000 secrets detected across these four open-source platforms.
Rise in Telegram cryptominers: Russian security firm Dr.Web is seeing a rise in crypto-mining trojans hidden in pirated software spread via Telegram.
Inferno Drainer: Group-IB estimates that the operators of the Inferno Drainer phishing service stole more than $80 million worth of assets from victims. The service shut down in November.
SonicWall exposure: More than 178,000 SonicWall firewalls across the world are still unpatched and vulnerable to one of two major vulnerabilities disclosed ten months ago, in March 2023 (CVE-2022-22274 and CVE-2023-0656). The figure represents more than three-quarters of all internet-exposed SonicWall firewalls, according to a scan conducted by security firm BishopFox. Researchers warn that attacks could be imminent after proof-of-concept code is published online.
Malware technical reports
Atomic Stealer: eSentire security researcher Russian Panda has analyzed AMOS, or Atomic Stealer, one of the first infostealers specifically created for macOS systems. Atomic is sold for the whopping price of $3,000/month, which makes it one of the most expensive malware strains offered today.
Pure malware family: ANY.RUN researchers have published a report on all the malware strains part of the Pure malware family. This includes PureMiner (cryptominer), PureLogs (infostealer), PureLogs Loader (loader), and PureCrypter (crypter, and probably the most known of the four).
DarkGate: South Korea security firm S2W Talon has published a report on DarkGate, one of today's most popular MaaS portals and malware loaders.
Androxgh0st: The FBI and CISA have published a report on Androxgh0st, a botnet malware specialized in attacking web and cloud infrastructure.
Sponsor Section
A short demo on how to use Panther's Detections-as-Code (DaC) platform for cryptominer investigations.
APTs, cyber-espionage, and info-ops
Connect Secure mass-exploitation: More than 1,700 Ivanti Connect Secure VPN appliances have been compromised using two recently disclosed zero-days. The devices were compromised by a Chinese state-sponsored group that has been using the zero-days since early December. According to security firm Volexity, the APT group ramped up operations on January 10 after Ivanti publicly warned customers of the two vulnerabilities. Patches for the two zero-days are expected on January 22. Several security researchers who've been tracking the attacks say that customers who did not apply Ivanti's temporary mitigations are most likely compromised already. More than 6,800 Connect Secure (formerly Pulse Secure) servers are currently exposed online and vulnerable to attacks.
Vulnerabilities, security research, and bug bounty
PAX POS vulnerabilities: STM Cyber has found six vulnerabilities in Android-based PAX POS devices. The company has published details on five of the six.
LeftoverLocals vulnerability: Security firm Trail of Bits has discovered a vulnerability that affects GPU cards from AMD, Apple, Qualcomm, and Imagination. Named LeftoverLocals, the vulnerability allows threat actors to memory isolation and recover data from other processes running on the same GPU. Trail of Bits says that while LeftoverLocals impacts the security posture of GPUs as a whole, the vulnerability is particularly dangerous for GPU platforms that run LLMs and ML models.
PixieFail vulnerabilities: French cybersecurity firm Quarkslab has identified nine vulnerabilities in EDK II, an open-source implementation of the UEFI standard. Codenamed PixieFail, the vulnerabilities reside in the EDK II network stack. Quarkslab says the bugs can be exploited by remote attackers during a computer's boot-up process to execute malicious code, poison DNS records, or hijack network sessions.
Opera MyFlow vulnerability: Security researchers have discovered a major vulnerability in MyFlow, a feature of the Opera browser that lets users sync files between devices. Attackers can abuse the feature to execute malicious files without user interaction on both Windows and macOS systems. Guardio Labs say Opera fixed the attack on November 22, but they are not releasing any proof-of-concept because of concern that Opera's existing browser architecture remains at high risk for exploitation.
Chrome zero-day: Google has released an update for its Chrome browser to fix an actively exploited zero-day tracked as CVE-2024-0519.
Citrix zero-days: Citrix has released security updates to patch two zero-days in NetScaler ADC and NetScaler Gateway appliances. Tracked as CVE-2023-6548 and CVE-2023-6549, the two are described as authenticated remote code execution and denial of service vulnerabilities. The company says it observed exploits for both CVEs against devices in the wild.
VMWare security update: Software vendor VMWare has published a security update to fix a missing access control vulnerability in its ARIA product line. The vulnerability (CVE-2023-34063) has a severity score of 9.9/10 and can allow unauthorized access to customer systems.
Atlassian security update: Atlassian has published a security update to patch 29 vulnerabilities across several of its products. The worst of these bugs is a template injection vulnerability that allows unauthenticated, remote attackers to run malicious code on Confluence servers. Tracked as CVE-2023-22527, the vulnerability received a rare 10/10 severity score. Atlassian says the bug impacts all Confluence servers part of its 8.x series released before December 5, 2023.
Infosec industry
New tool—KEV Detector: Security firm Ostorlab has released KEV Detector, a tool that automates the detection of known exploited vulnerabilities. It is sourced from CISA's KEV database but also Google Tsunami, Ostorlab's own Agent Asteroid, and some bug bounty programs.
New tool—SuperSharpShares: Security firm Lares has open-sourced a tool named SuperSharpShares that automates enumerating domain shares, allowing for quick verification of accessible shares in an associated domain.
New tool—iShutdown: Russian security firm Kaspersky has released iShutdown, a collection of Python scripts that can detect various strains of iOS spyware, such as Pegasus, Predator, and Reign.
Acquisition news: DevSecOps company Snyk has acquired AppSec runtime provider Helios.
Pwn2Own Vancouver 2024 program: The program for the spring version of Pwn2Own 2024 has been announced. Besides web browsers, virtualization software, servers, and enterprise software, this year, ZDI added a new cloud-native and container category. Slack has also been added to the target pool in the enterprise category. The cash prize pool is $1,000,000.
Risky Business Podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about how Stuxnet was an 'inevitability gamechanger,' how much we now know about the operation, and how much the Dutch government should have known at the time.