Risky Biz News: Proposed Web DRM could stop ad-blockers from working
In other news: Ransom payments fall to record low; tens of thousands of Citrix devices still unpatched for recent zero-day; and Target reveals its EasySweep skimmer detector.
This newsletter is brought to you by application allowlisting software maker Airlock Digital. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed. On Spotify:
A team of four Google engineers has proposed a new Web API named Web Environment Integrity that would allow websites to block client apps that modify their code.
In layman's terms, the proposal would force clients, such as desktop and mobile browsers, to cryptographically sign a CBOR token that contains details about their local environment.
Based on the token they receive, websites can then decide if they want to continue delivering service to the client or not.
The Web Environment Integrity API is couched as a security and privacy solution. The four Google engineers claim that websites will be able to detect when malicious modifications take place to code on the client side and allow websites to cut off malicious clients. The new API sounds like it could be ideal for blocking certain types of threats, such as banking trojans and phishing sites. The developers include several scenarios that could be mitigated with their new API:
Detect social media manipulation and fake engagement.
Detect non-human traffic in advertising to improve user experience and access to web content
Detect phishing campaigns (e.g., webviews in malicious apps)
Detect bulk hijacking attempts and bulk account creation.
Detect large-scale cheating in web-based games with fake clients
Detect compromised devices where user data would be at risk
Detect account takeover attempts by identifying password guessing
But while this sounds all fine and dandy, people far smarter and more accustomed to Google's BS than me have also pointed out the new API is a poisoned pill. Besides the obvious security pluses, the new API will also allow Google and money-grubbing website operators to effectively kill ad-blockers.
Because the new API can detect modifications to a website's resources, the API can be used to detect when an ad blocker is messing with advertising code and allow the site operator to stop delivering service.
This is why the new API has been informally named a "Web DRM" and for good reasons.
As Riot Games software engineer Michał Kawalec explains, the way this is being presented is also incredibly misleading. The authors are doing all they can to hide the fact that the new API is just Google's latest attempt to poison web standards just to preserve their advertising business.
"The proposal was presented as if emanating from four individual engineers who just happen to work at Google. Published to their private GitHub," Kawalec wrote on Mastodon.
"It's only when issues are raised where additional Googlers descend, reminding everyone that concerns need to be raised civilly and in a way Google accepts, otherwise any dissenting voices would be banned.
"And all of that is done not in the name of progress, social cohesion or any ideals, but to just sell some more mediocre ads," Kawalec says.
In a HackerNews comment, Codemix founder Charles Pick reinforces Kawalec's analysis.
"The underhanded way this is being proposed is really something else. It's hosted on a non-Google GitHub to provide distance, it's worded in a way that makes it seem like this is something that benefits users, when it's the absolute opposite of that. It subverts the whole concept of a user agent. This is a huge threat to our industry and we cannot allow this to happen."
And the criticism does not end here. A StackDiary blog post also raises the issue of possible monopolization. With Google, Amazon, and Meta code being loaded in a bunch of places, this would effectively give these services power to control attestation on most websites.
"By controlling the 'attesters' that verify client environments, Google, or any other big tech company, could potentially manipulate the trust scores, thereby deciding which websites are deemed trustworthy. This opens up a can of worms regarding the democratic nature of the web," Alex Ivanovs writes.
To say that the response to the proposal has been negative would be a gross misrepresentation of what has happened on the project's GitHub Issues page, where barring 5-6 entries that actually raise an issue, most of the reports take shots at the API and Google itself.
And the shots are actually well-deserved. Remind you, this is the company that reworked Chrome's extensions API for the sake of security but accidentally happened to neuter the effectiveness of those evil ad-blocker extensions hurting its ad business.
This is also the company that shipped an ad-blocker built into the Chrome browser that doesn't actually block any ads.
This is also the company that doesn't moderate its own advertising platform allowing a flood of malicious ads to flow through just because money from threat actors has the same color and smell as money from legitimate customers.
This is also the same company that doesn't remove malicious Chrome extensions unless some reporter writes an article about it, and that article starts trending on social media.
The general sentiment is that many people are now starting to see through the company's tactics at this point.
Breaches, hacks, and security incidents
TOMRA cyberattack update: Thousands of TOMRA recycling machines have been offline for almost a week after the company was hit by a mysterious cyberattack. The vast majority of affected systems are in the Netherlands. Customers can still deposit plastic bottles, but the company can't connect to any of its machines anymore. In an update, TOMRA says the attackers gained access to its network from a Montreal location and then spread to the rest of its network. Although the incident looks like ransomware from the outside, TOMRA says they found no evidence of encryption and have not received any ransom. [Additional coverage in Parool]
Telekom Malaysia data breach: The personal details of millions of Telekom Malaysia customers were stolen in a security breach. The company says hackers stole historical data from its Unifi service. [Additional coverage in New Strait Times]
VirusTotal leak: Google has apologized after an employee accidentally uploaded a CSV file with the account details of 5,600 of its customers on the VirusTotal platform, exposing their information to anyone with a VT account.
"We removed the file, which was only accessible to partners and corporate clients, from our platform within one hour of its posting."
Conic Finance hacked twice: Cryptocurrency platform Conic Finance was hacked twice on two consecutive days over the past weekend. The company first lost $3.26 million worth of assets on Friday and then lost another $300,000 on Saturday. The two incidents are unrelated, and the first exploited an Oracle attack against one of its smart contracts, while the second was a reentrancy vulnerability in a different one. The company has posted a post-mortem of both hacks.
AlphaPo crypto-heist: Hackers have stolen more than $23 million worth of crypto-assets from cryptocurrency payments provider AlphaPo. The funds were stolen from the company's hot wallets and included assets such as Bitcoin, Ethereum, and Tron. The breach took place on Sunday, July 23, and the company has yet to confirm the hack. [Additional coverage in CryptoHeadlines]
Microsoft hack: Cloud security firm Wiz says that the MSA signing key stolen by Chinese hackers during their recent Microsoft hack could have granted them access to a multitude of other Microsoft core services. Wiz says the stolen key could not only sign authentication tokens for Microsoft email servers but could also be used to sign OpenID 2.0 tokens for any Azure AD applications.
"The full impact of this incident is much larger than we Initially understood it to be. [...] At this stage, it is hard to determine the full extent of the incident as there were millions of applications that were potentially vulnerable, both Microsoft apps and customer apps, and the majority of them lack the sufficient logs to determine if they were compromised or not."
OnlyFans DDoS: Pro-Kremlin "hacktivist group" Anonymous Sudan has DDoSed the OnlyFans platform. They have crossed a line! Put these scumbags in jail! [Additional coverage in Cyberscoop]
General tech and privacy
FTC & HHS warning on web analytics: The Federal Trade Commission and the US Department of Health and Human Services have issued a joint advisory that warns hospitals about the dangers of using online tracking solutions like Google Analytics and Meta Pixel on their websites and mobile apps. The two agencies warn that improperly configured web analytics solutions could lead to sensitive healthcare data being sent and stored on remote servers. The two agencies sent a joint letter [PDF] to approximately 130 hospital systems and telehealth providers to alert them about the risks.
Government, politics, and policy
EU's Cyber Resilience Act: The European Union has approved a draft version of the Cyber Resilience Act, a set of new cybersecurity-related rules for IoT devices. The act passed the EU's Industry, Research, and Energy Committee with 61 votes in favor, one against, and 10 abstentions. Under the new regulations, vendors will have to ensure their products meet a certain set of criteria before being sold in the Eurozone. Products will have to come with automatic security updates as the default option, must ensure data confidentiality using encryption, and vendors must inform authorities of any attacks. The new rules are expected to enter into effect by 2024.
White House on AI: The White House and seven leading AI companies have agreed to work on a set of industry best practices when it comes to developing and rolling out artificial intelligence solutions.
DOJ merges NCET into CCIP: The US Department of Justice has merged its cryptocurrency crime team into its cybercrime unit. Founded in 2021, the National Cryptocurrency Enforcement Team is now formally part of the DOJ's Computer Crime and Intellectual Property Section. The Department justified its decision by the need to have the two divisions work more closely because most cybercrime also involves a cryptocurrency laundering component and because its crypto-crimes team also needs more human resources to investigate all the incidents. [Additional coverage in NextGov]
Expeditionary cyber forces: Lt. Gen. Timothy Haugh, the nominee to become the next head of the NSA and CyberCom, has pledged to create "expeditionary cyber forces" that can be deployed and reach important tactical targets in forward locations. [Additional coverage in DefenseScoop]
Malicious code on Chinese devices: South Korea's National Intelligence Service (NIS) says it found malicious code inside measuring equipment manufactured in China and used by government agencies. The malicious device was discovered in June, and the incident triggered a full NIS audit of Chinese-made devices used in government agencies, such as networking equipment and CCTV systems. The agency says that 30% through its audit, they found an additional suspicious device but did not provide additional details. [Additional coverage in Hani]
Sponsor section
In this Risky Business News sponsor interview, Catalin Cimpanu talks with Airlock Digital founders Daniel Schell and David Cottingham about vulnerable drivers, BYOVD attacks, and the problem with driver-based attacks.
Cybercrime and threat intel
Sachkov case: Former Group-IB CEO Ilya Sachkov is scheduled to receive a verdict in his treason case this week on Wednesday, July 26. Sachkov was detained in Moscow in September 2021 and charged with treason for providing details on Russian hackers to foreign intelligence services. After two years of pre-trial detection, a judge heard his case earlier this month. Sachkov pleaded not guilty, and his lawyer asked for an acquittal, while Russian state prosecutors have requested 18 years in prison. [Additional coverage in DW]
Supply chain attacks on banks: DevSecOps company Checkmarx says it discovered malicious libraries on the npm repository that suggest threat actors attempted two separate supply chain attacks against the banking sector in the first half of this year. In the first incident, the attackers uploaded malicious npm libraries on the npm portal, posing as a bank's employees. In the second, the attackers crafted a malicious library that would only activate its malicious code if it would ever be used on a bank's mobile login page. Checkmarx says that while they saw attempts to carry out supply chain attacks via the npm portal before, these are the first incidents that specifically targeted the banking vertical.
Phishing campaign targeting students: Proofpoint researchers have spotted a financially-motivated cybercrime group targeting university students with a phishing campaign peddling job offers. The campaign has been active since March 2023 and has focused on bioscience and healthcare students. The threat actor tries to entice recipients to have a video call, with the end goal being to convince applicants to pay a hefty job application fee, in a scam known as advance fee fraud (AFF).
SpyNote campaign: A smishing campaign is targeting electric and water utility users in Japan with the SpyNote Android RAT.
Zyxel DDoS botnet: Fortinet says they've discovered a DDoS botnet being assembled using Zyxel devices that have been compromised with CVE-2023-28771, a vulnerability in its firewalls the company patched back in April.
BreachForums clone: Another BreachForums clone is now available at breachforums[.]is. Start the countdown until it gets hacked or seized by authorities.
Clop: Fortinet has published a profile on the Clop ransomware gang.
New npm malware: Thirty-one malicious npm packages were discovered last week. Check out GitHub's security advisory portal for more details.
Ransom payments fall to record low: In the second quarter of 2023, the percentage of ransomware attacks that resulted in the victim paying fell to a record low of 34%. Security firm Coveware puts the fall on companies continuing to invest in cybersecurity and incident response training. The previous low was 37%, recorded in both Q3 and Q4 of last year. The number is more than half of the 85% Coveware recorded in Q1 2019 when it first started tracking the stat. The company also estimates that the Clop gang stands to earn between $75-100 million dollars just from the MOVEit campaign.
Malware technical reports
RootTeam: OALABS has IOCs on a new Go-based stealer advertised on Telegram and named RootTeam.
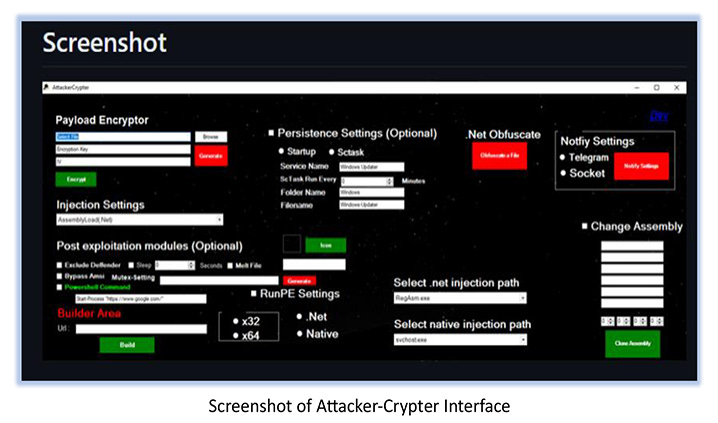
Attacker-Crypter: CyFirma has a breakdown of Attacker-Crypter, a new crypter that has been gaining popularity in recent months.
Sponsor Demo
Airlock Digital CEO David Cottingham shows Patrick Gray how Airlock's execution control and allowlisting solution works.
APTs and cyber-espionage
Storm-0558: Add Nicholas Burns, the US Ambassador to China, as a victim of the recent Storm-0558 hack of Microsoft email accounts. [Additional coverage in WSJ/non-paywall]
APT31's industrial espionage foray: Russian security firm Kaspersky says that it observed the APT31 Chinese cyber-espionage group target industrial organizations across Easter Europe in 2022. The company says the group used a new malware strain named MeatBall but also new versions of the FourteenHi malware—typically used in espionage operations against government entities.
Vulnerabilities, security research, and bug bounty
Citrix zero-day: CISA has released a technical report on CVE-2023-3519, an actively-exploited zero-day in Citrix ADC and NetScaler gateway devices the company patched last week. According to CISA, observed attacks have dropped web shells on the compromised servers. The agency identified one of the victims as a US critical infrastructure organization. Google's Mandiant division says the attacks are consistent with Chinese espionage operations but has no tangible evidence to officially link the attacks to a particular group. Aussie security firm Assetnote has also released its own analysis of the vulnerability. Security firm BishopFox says that from the 61,000 Citrix appliances exposed on the internet, roughly 32,000 have not been patched for this recent vulnerability. Shadowserver puts the same number at around 15,000.
Chrome zero-day details: More details have emerged about a Chrome zero-day (CVE-2023-3598) that was patched back in June. According to TechCrunch, the zero-day was discovered and used by an Apple engineer at the HXP CTF contest earlier this year but never reported to Google by the person who used it. The bug was eventually reported to the browser maker by another contest participant, who also received the reward for it.
Metabase security update: The Metabase analytics platform has told customers to "immediately" update their servers to fix what the company calls an "extremely severe" security flaw. Metabase says the vulnerability allows an unauthenticated attacker to run arbitrary commands on the server where the Metabase analytics server is installed, leading to a full server takeover. The company says the vulnerability was privately reported and has seen no active exploitation in the wild. A CVE identifier will be released in roughly two weeks.
Atlassian security updates: Atlassian patched three vulnerabilities last week in its Confluence and Bamboo products. All three are RCEs.
"These vulnerabilities are discovered via our bug bounty and pen-testing processes, as well as 3rd party library scans."
Cisco SPA forever-day: A security researcher known as Darren (or FullSepctrum) has published details and a PoC for CVE-2023-20126, a vulnerability in Cisco SPA112 phone adapters that the company declined to patch back in May this year. Hence, why they called it a forever-day.
EasySweep: Target's cybersecurity team has developed and patented a novel device that can be used to discover payment terminal skimmers. Named EasySweep, the device is a simple plastic mold that Target employees can insert inside the card slot of an in-store payment terminal. If the device fits, the terminal is safe to use. If it doesn't, security teams are mandated to check for the presence of a skimmer inside the card slot that may be blocking the EasySweep device. Target says it shipped more than 60,000 EasySweep devices to its stores, where the device has been used to perform daily terminal security checks for the past three years.
Infosec industry
New tool—PassDetective: Turkish security researcher Yunus Aydin has open-sourced a tool named PassDetective that scans your shell command history for mistakenly written or copy-pasted passwords, API keys, and secrets that got recorded in there by accident.
New tool—DroneXtract: Hardware researcher Angelina Tsuboi has open-sourced DroneXtract, a digital forensics suite for DJI drones. It can analyze sensor values, visualize flight maps, and audit for criminal activity.
New tool—CVE-2023-3519 Inspector: Security researcher Bryan Smith has released a tool named CVE-2023-3519 Inspector that can scan and detect Citrix ADC and NetScaler devices that are vulnerable to the recent CVE-2023-3519 Citrix zero-day.
AWS re:Inforce videos: Talks from the AWS re:Inforce 2023 security conference, which took place in mid-June, are now available on YouTube.
Risky Business Podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq look at the idea of actively shaping ransomware group behavior to get the type of behavior we'd prefer.