Risky Biz News: Russian radio stations hacked to blast fake air raid warnings
In other news: Food giant Dole down for two weeks after ransomware attack; Gate crypto-platform hid major hack for years; Google's Play Store privacy labels are just as inaccurate as Apple's.
This newsletter is brought to you by Airlock Digital, Proofpoint, runZero, and Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed.
Several radio stations across multiple Russian cities were hacked this Wednesday (February 22) to broadcast air raid warnings.
The air raid alerts were heard in Belgorod, Kazan, Novosibirsk, Magnitogorsk, Penza, Ufa, Voronezh, Nizhny Novgorod, Tyumen, Izhevsk, and other cities, according to reports from Vedomosti and SbirMedia.
Multiple radio stations were hacked, including the likes of Relax FM, Humor FM, Business FM, Like FM, Comedy FM, Romantika, Avtoradio, Radio Energy, and Children's Radio. According to RIA, many of the stations were part of Gazprom Media, which may offer a clue on how the hackers managed to blast the fake air raid warning at about the same time.

Russian local officials called the incident "a provocation by supporters of the Kyiv regime."
The Russian Ministry of Emergency Situations confirmed the hack in a Telegram post, but they did not share any info on the attack or any attribution.
This is not the first time suspected Ukrainian hackers have hacked Russian radio stations. In June 2022, one such hacker hijacked Kommersant's FM radio to blast the Ukrainian anthem and anti-war songs, forcing the company to temporarily shut down its air programming and broadcast solely via the internet for a few hours.
Two months later, in August 2022, Ukrainian hackers hijacked security cameras across the occupied Crimea and Donbas to play patriotic Ukrainian music on Ukraine's Independence Day.
Breaches and hacks
Gate.io hid a 2018 hack: Cryptocurrency exchange Gate.io hid a major hack that took place in April 2018 when the company had its hot wallet compromised by North Korean hackers and lost $230 million worth of assets. The hack was discovered last November by a blockchain investigator named ZachXBT but only got widespread attention this week after the hackers moved $3.2 million worth of Ether to new addresses.
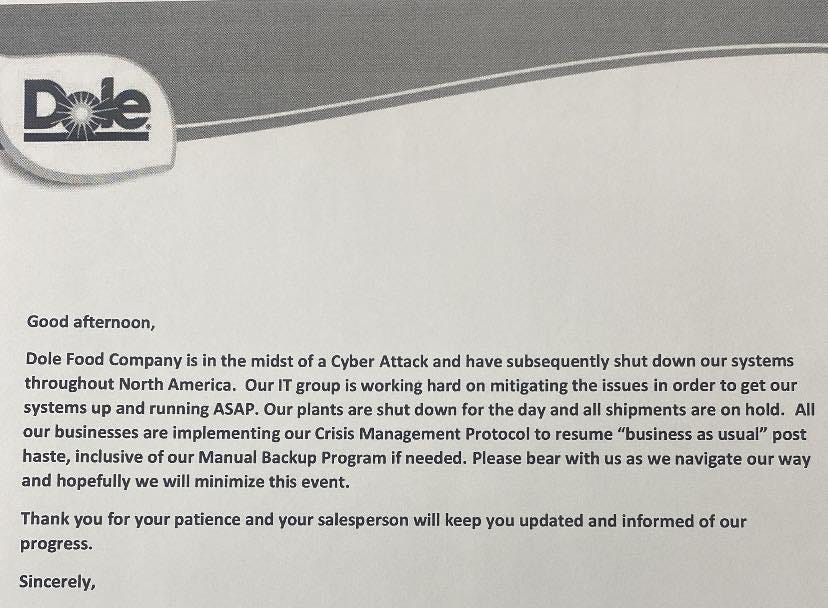
Dole ransomware: A ransomware attack has forced agricultural and food production giant Dole to shut down its food packaging and distribution operations across North America. The incident took place earlier this month and impacted the company's ability to ship ready-to-eat salad kits across the US. According to CNN, Dole disclosed the incident to retailers once it took place, but two weeks later, the company's operations are still down across the US.
General tech and privacy
Valve's Dota2 honeypot catch cheaters: Gaming company Valve has banned over 40,000 Dota2 accounts using a game patch that introduced a honeypot that caught their cheating software. Valve says the cheating tool used a Dota2 exploit to allow cheaters to read game data that would not show up on the screen during normal gameplay. Through a recent update, Valve says it patched the exploit but also added a honeypot system to keep the data available but also log which user accounts accessed it. Valve says that each account banned this week continued to read this data following its patch and that each ban handed out was "well-deserved." Also, in good news for gamers everywhere, Activision has also won a civil case it filed against the company behind EngineOwning, the most popular cheating tool for the Call of Duty franchise. A judge ordered EngineOwning to pay Activision $3 million in damages.
Twitter Blue already abused (or used as intended): Internet and big tech research group Reset says that Russian propaganda networks are buying Twitter Blue subscriptions to promote and spread misinformation about the Ukrainian war atop people's timelines. The discovery comes after several misinformation experts warned Musk last year that the feature would be abused this way. According to a Reset report shared with the Washington Post, most of these accounts are brand-spanking new, created last year after Russia's invasion of Ukraine, and focus on spreading messages from Russian politicians and its media. But the actual discussion here is about the potential and the very likely possibility of oppressive governments funneling money into Twitter's accounts for its silent and complicit consent to carry their garbage propaganda.
"The accounts claim to be based outside of Russia, so they can pay for verification without running afoul of US sanctions. But they pass along articles from state-run media, statements by Russian officials, and lies about Ukraine from Kremlin allies."
Meta CIB report Q4 2022: Meta says it suspended covert influence networks operating inside Bolivia, Cuba, and Serbia at the end of last year. Meta says each network focused exclusively on local audiences and were linked to governments or ruling parties in their respective countries. The networks typically posted content praising their local governments and criticizing the opposition. In addition, Meta says that throughout last year, most Russian influence operations appear to have lost their effectiveness, becoming "low-quality." The company, which has shut down tens of such operations in the past, says it has seen Russian influence networks slowly shift to other social media platforms as their main mediums of interaction.
Play Store privacy labels are inaccurate: A Mozilla study has discovered that a large part of the 40 most popular free and paid apps on the Google Play Store display inaccurate privacy labels. Mozilla says the app makers, which are the ones that decide what privacy labels to show on their apps, are misleading users into thinking their data is safe or won't be shared with third parties. This seems to be the case even when at a closer look at some apps' privacy statements, they clearly say they will collect and share data with other parties, contradicting their own privacy labels. Mozilla blames the current situation and the state of the misleading labels on Google, which "appears to absolve itself of the responsibility to verify the information the apps provide." An April 2022 study found similar issues with Apple's App Store and its "privacy nutrition labels."
Government, politics, and policy
CR14 exercise: Three British military intelligence teams won Defence Cyber Marvel 2 (DCM2), the biggest military-led cyber exercise in Western Europe. The exercise was hosted in Estonia's CR14 cyber range and hosted 750 cyber specialists organized in 34 teams from 11 countries. The UK's 7 Military Intelligence unit won the contest, followed by the 5 Military Intelligence unit, and Welsh Water in third.
App ownership initiative: Florida Attorney General Ashley Moody wants Apple and Google to notify users if an app they are about to install is owned by a foreign entity. In letters sent to both the Apple and Google CEOs, Moody wants the companies to place visible designations on foreign-developed or foreign-owned mobile apps from countries that may pose a national security risk to US consumers, such as China and Russia.
EU Commission TikTok ban: The EU Commission has ordered employees to remove the TikTok app from their work devices. EU Commissioner Thierry Breton says the ban was driven by cybersecurity concerns and the company's Chinese ownership. The move comes after the US also banned TikTok use on government devices at the end of last year.
NSA guidance on securing home networks: The US National Security Agency has published a guide on how employees working from home can secure their local home networks against threat actors. The guide [PDF] includes recommendations for securing routers, implementing WiFi network segmentation, securing webcams and browsers, backup recommendations, and more.
Sponsor section
Thinkst is one of this newsletter's four main supporters and this week's featured sponsor. The company has recently launched a new type of canary token that looks like an Azure login token and warns companies whenever a threat actor tries to use them.
Cybercrime and threat intel
Forsage founders charged: US authorities have charged the four founders of the Forsage DeFi cryptocurrency platform for running a Ponzi scheme and stealing more than $340 million from their investors. All four are Russian nationals and still at large.
NLBrute author detained and charged: US authorities have charged Dariy Pankov (aka dpxaker), the creator of NLBrute, a hacking tool for decrypting (cracking) login credentials. Pankov, who is a Russian national, was detained in the country of Georgia last October and extradited to the US, where he was arraigned in court this week. US officials say Pankov sold the login credentials for more than 35,000 compromised systems on a dark web marketplace. He supposedly made more than $350,000.
Backdoor backup servers: Cybersecurity firm Fox-IT has discovered a major hacking campaign that has successfully compromised more than 280 enterprise backup servers with a dangerous backdoor. The attacks began in late November of last year and exploited a vulnerability (CVE-2022-36537) in the ConnectWise R1Soft backup server. Fox-IT says it discovered the campaign at the start of the year and has silently worked with the Netherlands' cybersecurity agency to notify server owners. Researchers say that from the 286 servers they found compromised earlier this year, they have now managed to get the number down to 146 at the start of this week. Fox-IT says this campaign is dangerous because once the attacker gains control over the R1Soft central backup server, they can also deploy malware to all R1Soft backup agents inside a company, attacks that can easily be used to mass-deploy ransomware.
KEV update: CISA has updated its KEV database with three new vulnerabilities that are currently being actively exploited. The first is CVE-2022-47986, an unauth RCE in IBM Aspera Faspex servers that came under exploitation earlier this month. The other two are two vulnerabilities (CVE-2022-40765 and CVE-2022-41223) in Mitel VoIP appliances. Details about these latter attacks are unknown, but ransomware gangs have been known to target them to enter corporate networks.
Telegram hacking: OCCRP investigator Jurre van Bergen claims to have discovered the loophole used by Israeli mis/disinformation seller TeamJorge to hijack and gain access to Telegram accounts. The company allegedly used this method to hack into Telegram accounts and leak real/edited conversations from a customer's political opponents.
Spam attack on npm: The npm package repository has been flooded with nearly 15,000 malicious npm libraries that contain phishing links in their descriptions. Some of the links also tried to lure visitors to retail websites where the attacker would profit from referral programs. DevSecOps company Checkmarx says the spam attack was sudden and took place overnight, being similar to a campaign they spotted in December of last year. That campaign was far larger, hitting npm, PyPI, and NuGet with more than 140,000 spammy packages.
PyPI malware: Researchers with ReversingLabs have identified 41 malicious Python libraries uploaded on the official PyPI portal. All of the packages posed as libraries meant to provide HTTP processing capabilities. ReversingLabs says the libraries contained code to steal data from a local system and deploy additional malware. The same campaign was also spotted by Fortinet as well.
Zarya: A new pro-Russian hacktivist group named Zarya is building DDoS botnets with custom versions of the Mirai malware to use in attacks against western targets. Radware says the group split from the larger Killnet group and is working with another group called Akur to develop and host the botnets. Akur, in general, provides hosting services to many of the pro-Kremlin "hacktivist" groups.
NFT phishing campaign: The security team of the ZenGo cryptocurrency wallet says it discovered a suspected North Korean hacking group behind a campaign that stole almost $25 million worth of NFTs from their owners. ZenGo says the threat actor used a novel offline signature attack to steal ERC-20 tokens and take control of the wallets associated with the NFTs. ZenGo says the group's attacks had ties to phishing infrastructure previously linked to North Korean groups. ZenGo says the attack was carried out by the same North Korean group that was seen stealing NFTs last year by blockchain security firm SlowMist.
YouTube-hosted campaign: SilentPush has published details about a threat actor's campaign that uses compromised YouTube accounts to host videos promoting software cracks and pirated software in order to get users to install malware-laced apps. These apps typically contain an infostealer that pilfers a user's local credentials. Infostealers used in this campaign include the likes of Burmilia, Redline, and Rhadamanthys.
Malware technical reports
Libgcc_a miner: Chinese security researchers have analyzed a new crypto-mining malware strain named libgcc_a. Besides mining, the malware can also brute-force other hosts and help spread its botnet. Researchers say the malware can run on Windows, Linux, macOS, and FreeBSD platforms alike.
S1deload Stealer: Bitdefender has discovered a new infostealer malware strain named S1deload Stealer that is currently being distributed in the wild. S1deload Stealer works like any other stealer, infecting computers and stealing a user's locally stored passwords. However, Bitdefender says the stealer also uses infected PCs as bots for farming YouTube views, spamming on Facebook pages, and mining cryptocurrency. Bitdefender says it is currently detecting more than 600 infected users at the time of writing.
Bumblebee spam: Security firm Zvelo has a report on a recent wave of WeTransfer and Smash spam that has been delivering the BumbleBee malware.
macOS cryptominer: Jamf researchers have spotted a malware campaign targeting macOS users with a cryptominer disguised in pirated software.
Phobos ransomware decrypter: CERT-PL has developed a decrypter for Phobos, a ransomware strain first spotted in the wild in 2019. However, despite their achievement, CERT-PL says their tool is "impractical to use" as it requires an in-depth study of each victim's encrypted data and powerful computing resources. Furthermore, not every Phobos version can be decrypted by the method they developed.
Black Basta ransomware: We also had this week a nice report on the Black Basta ransomware by the team at Zscaler.
APTs and cyber-espionage
Rattlesnake: Weibu researchers have published a report on the Rattlesnake APT attack that targeted a Chinese university and various Pakistani organizations.
SideCopy: On the same note, Chinese security firm Rising says it spotted a campaign from the SideCopy APT targeting an Indian government department.
Hydrochasma: Broadcom's Symantec has spotted a new APT group, which it named Hydrochasma, targeting medical and shipping organizations across Asia. The attacks, which have relied exclusively on open-source tools, have been going on since October 2022.
Clasiopa: The same Symantec team also has a report out on another new APT named Clasiopa (suspected StoneFly activity). This one uses a custom backdoor named Atharvan and has been seen targeting a materials research organization in Asia. Symantec has not attributed any of these groups so far.
Vulnerabilities and bug bounty
DedeCMS zero-day: Chinese security firm NGC660 has discovered a zero-day vulnerability in DedeCMS, a PHP-based content management system popular in China. No patches as of yet.
Cisco security updates: Cisco has released seven security updates.
LogicalDOC vulnerabilities: WhiteOak Security has disclosed details about four vulnerabilities in the LogicalDOC document management system.
Fortinet PoC: Last week, Fortinet patched a major vulnerability (CVE-2022-39952) in its FortiNAC firewalls. There's now a PoC for it.
Oh, noes! The bug is under active exploitation! Who could have seen this coming!?!
Google VRP payouts: Google says that in 2022, the company paid more than $12 million to security researchers in the form of bug bounty rewards via its Vulnerability Research Program. The figure represents the highest number paid by Google to security researchers so far and the second-highest figure paid by a tech company to security researchers throughout a calendar year, second only to Microsoft, which paid $13.7 million via its bug bounty program last year. Google says that $4.8 million of the total sum went to its Android bug bounty program, including a single $605,000 reward for an Android security flaw that represented the largest bug bounty reward Google ever handed out.
Infosec industry
AT&T cybersecurity division: US media company AT&T is exploring the sale of its cybersecurity division in order to pay down debt following its $108.7 billion acquisition of Time Warner Inc in 2018.
New tool—AWS Break Glass Role: Amazon has released a tool to create a special AWS user account to use in "break glass emergency" situations, such as breaches or misconfigurations.
New tool—SMAT Network Graph: The team behind the Social Media Analysis Toolkit (SMAT) has launched its Network Graph tool in a closed beta. SMAT says Network Graph is an interactive "point-and-click" tool to find influence and dis/misinformation campaigns across multiple social networks. [UPDATE: The tool has been renamed Open Measures in December 2023.]
Intel471 CEO steps down: Mark Arena will step down at the end of the month from his role as CEO of cybersecurity firm Intel471. Arena will remain an advisor and a member of the board. Intel471 co-founder Jason Passwaters will take on the CEO role going forward. Arena served as CEO for nine years.
Risky Business podcast host Patrick Gray recorded this video with Okta, which shows users how to enable phishing-resistant authentication. It also goes into how enabling phishing-resistant auth for some users can benefit the whole org, even if it's not turned on everywhere.